Multi-layer System Security Explained
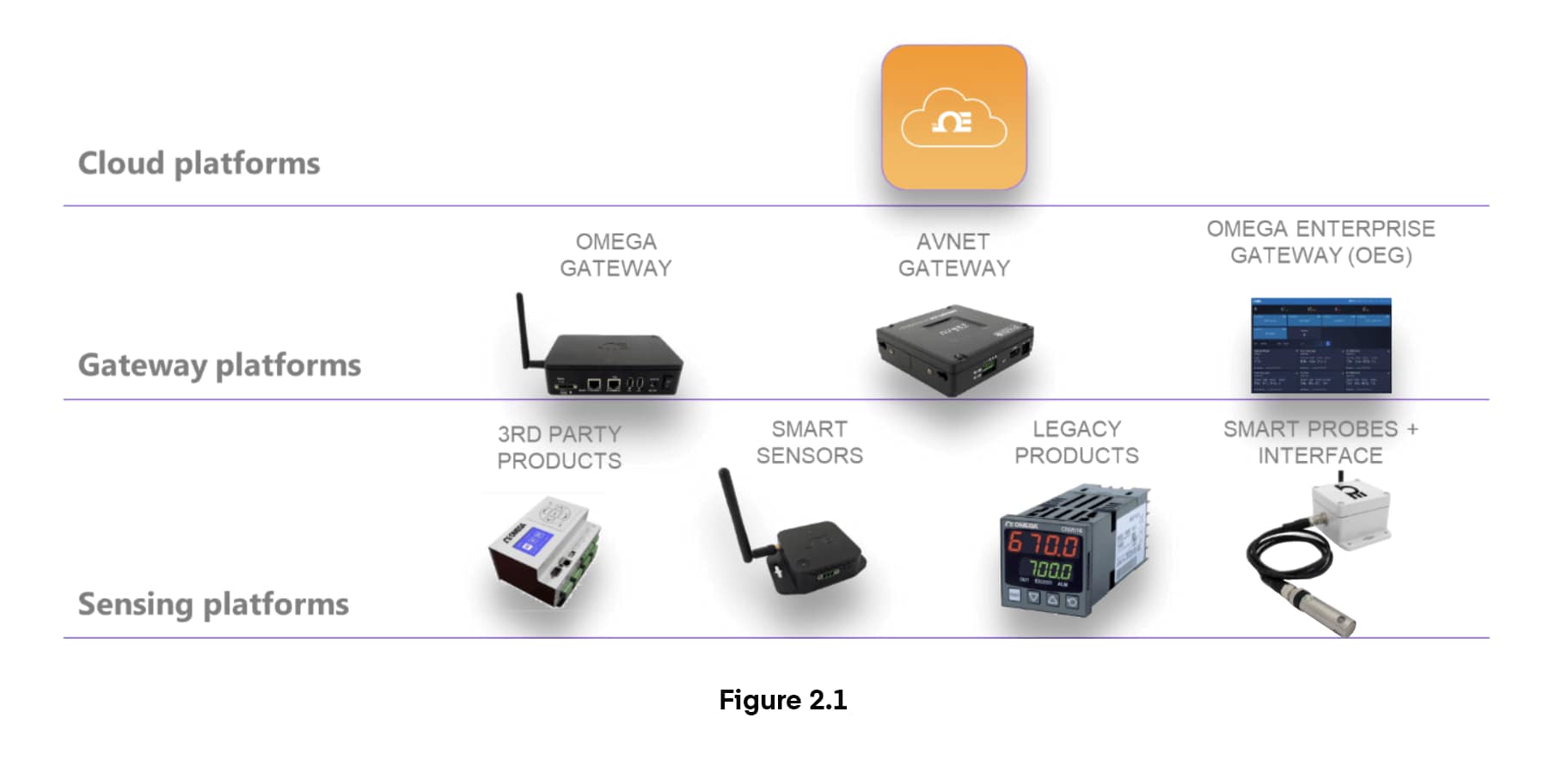
Smart manufacturing and Industry 4.0 have created a convergence between information technology (IT) and operational technology (OT) systems. When considering implementing a system of IIoT sensors, it’s important to understand potential security risks and challenges and ensure those vulnerabilities are proactively addressed.
Securing an IIoT system by design requires a multi-layered approach. The Omega IIoT Link ecosystem incorporates threat-mitigating security in every zone, from sensors to gateway communications to the cloud.
Multi-Layer Security Explained
1. Southbound Gateway/Sensor Connection
- IEEE 802.15.4 ECDH encrypted key agreement protocol
- Device Authentication
- Link Layer Encryption AES CCM
- Secure OTA download
- OTD firmware boot manager with Secure Boot
- Sensor identity cross-check
The southbound gateway-sensor connection uses the industry standard IEEE 802.15.4 AES256 encryption protocol, which features Elliptic Curve Diffie-Hellman (ECDH) encrypted key agreement protocol and device authentication to avoid man-in-the-middle (MiTM) attacks. Link Layer Encryption AES CCM (cryptoblock cipher mode)
- Secure Over The Air (OTA) download
- On The Device (OTD) firmware boot manager with Secure Boot - verifies the authenticity of the firmware to be executed on the device upon every boot
- Sensor identity cross-checked with cloud credentials, preventing spoofing
2. Northbound Cloud/Gateway Connection
- AMQP Protocol on TCP/IP
- Transport Layer Security (TLS) + authentication
- AES-256 encryption
- Private Keys with Trusted Platform Module (TPM) Gateway
- Unique challenge Codes
- Bidirectional authentication validation
- Authentication mode on the Gateway retained thru power cycles
- Security challenge mode after 5 failures
The northbound cloud/gateway connection uses the industry standard AMQP protocol on TCP/IP with Transport Layer Security (TLS), including a certificate-based authentication protocol with AES-256 encryption. It features separate shared private keys for Gateway and Cloud with a hardware-based Trusted Platform Module (TPM) in the Gateway. Unique challenge Codes generated by the Gateway and Cloud use a shared, non-published hash function from a common challenge code that is built from shared (encrypted) sensor information. Both the Gateway and Cloud validate that the authentication process has been successful. Authentication mode on the Gateway is retained thru power cycles. If the Gateway enters the authentication state, ALL subsequent accesses require either authentication or a factory reset. After 5 failed authentication attempts, the Gateway MUST be power cycled. Cloud access authentication goes into security challenged mode after 5 failures.
3. Cloud Layer
- Unique ID
- Accounts + passwords
- Microsoft Azure DDoS protection
- IoT Hub multi-level control, authentication and authorization
The cloud layer requires user accounts passwords and a unique ID to access data, and runs on Microsoft Azure which includes denial of service attack mitigation in the platform, and an IoT Hub with multiple levels of access control, authentication and authorization.
4. Final Validation
Finally, penetration (“white hat”) testing validates that there are no vulnerabilities in the implementation.
Conclusion
While no IIoT system guarantees immunity from every possible threat, the Omega IIoT Link system incorporates security as a core design feature at every layer to provide a robust ecosystem of safety. From encryption and authentication, communication safety protocols and password protection and white-hat testing/validation, Omega IIoT Link addresses security at every level of the system. For more information on Omega IIoT Link security, get a consultation today.
Glossary
Check out the definitions of technical terms and abbreviations used in this article.
AES CCM Encryption
Advanced Encryption Standard-Counter with CBC-MAC (AES CCM) is an authenticated encryption algorithm designed to provide both authentication and confidentiality.
AMQP Protocol
Advanced Message Queuing Protocol (AMQP) is an open standard application layer protocol for middleware message transmission.
DDoS
Distributed Denial-of-Service (DDoS) attacks are malicious attempts to disrupt a server or network by overwhelming it with internet traffic.
ECDH
Elliptic Curve Diffie-Hellman (ECDH) is an encrypted key agreement protocol that allows two parties to share information using either a shared secret key or a derivative key from the shared key, which can then be used to encrypt subsequent communications using a symmetric-key cipher.
MITM
A man in the middle (MITM) attack (also known as monster in the middle, machine in the middle, monkey in the middle, meddler in the middle and manipulator in the middle) is a cyberattack where the attacker intercepts (and possibly alters) private communications between two parties, unbeknownst to those parties.
TCP/IP
Transmission Control Protocol/Internet Protocol (TCP/IP) is a suite of communication protocols designed by the United States Department of Defense that enable application programs and computing devices to safely exchange messages over a network using data packets.
TLS
Transport Layer Security (TLS) is a cryptographic protocol to ensure communication security over a network. TLS uses encryption, authentication and session keys to secure the connection and ensure the authenticity of a communication.
TPM
A Trusted Platform Module (TPM) gateway uses a microcontroller to securely authenticate a device/platform. TPMs include multiple physical security mechanisms to make them tamper-resistant, and to ensure malicious software cannot tamper with security functions.